Multi-Cloud vs. Cloud-Agnostic: The Difference Matters
Running on two clouds usually means double the pain. True portability comes from open standards (K8s, Terraform) and abstraction layers, not just multiple accounts.
Author: CloudOpsPro Engineering Team
Category: Strategy, Architecture, Enterprise
Date: November 20, 2025
"We need to be multi-cloud to avoid vendor lock-in." This is the most expensive sentence a CTO can utter without a plan.
There is a massive difference between being Multi-Cloud (running workloads on AWS and GCP) and being Cloud-Agnostic (ability to move workloads seamlessly). Confusing the two leads to "Least Common Denominator" architecture, where you use the worst features of every cloud and the best features of none.
1. The Multi-Cloud Trap
True multi-cloud usually happens by accident (M&A) or poorly planned strategy.
The Complexity Multiplier:
- ** IAM:** AWS IAM roles vs GCP Service Accounts is a nightmare to map.
- Networking: VPC peering vs Google VPC functioning.
- Data Gravity: Moving 1PB of data from S3 to GCS costs ~$90,000 in egress fees.
If you build an app that natively uses AWS DynamoDB (proprietary) and Google BigQuery (proprietary), you are indeed "multi-cloud"—but you are double locked-in. You can't leave AWS or Google.
2. Cloud-Agnostic: The Real Goal
Cloud-agnosticism targets Portability.
To achieve this, you must rely on Open Standards, not proprietary Services.
| Layer | Proprietary (Locked-In) | Cloud Agnostic (Portable) |
|---|---|---|
| Compute | AWS Lambda, Fargate | Kubernetes (EKS/GKE/AKS) |
| Events | EventBridge, SNS/SQS | Kafka, NATS, RabbitMQ |
| Storage | S3 (API is effectively standard though) | MinIO (Self-hosted S3 compatible) |
| Database | DynamoDB, Aurora Serverless | PostgreSQL, MongoDB, Cassandra |
| IaC | CloudFormation | Terraform / OpenTofu |
The Trade-off: Being cloud-agnostic means you have to manage more yourself. You manage the Kafka cluster on K8s instead of just clicking "Create SQS". You pay for portability with operational overhead.
3. The "Abstracted" Platform Strategy
The winning strategy for large enterprises is building an Internal Developer Platform (IDP) that sits above the clouds.
The Stack:
- Uniform Compute: Kubernetes everywhere. Since K8s APIs are identical on AWS and Azure, your deployment manifests don't change.
- Uniform Traffic: A Service Mesh (Linkerd/Istio) handles mTLS and routing, so the underlying VPC differences matter less.
- Uniform CD: ArgoCD creates a GitOps workflow that pushes to any cluster, regardless of provider.
Example: Terraform Abstraction
Instead of writing raw AWS resources, write modules:
module "app_database" {
source = "./modules/postgres"
# Internally, this decides whether to spin up RDS (AWS) or CloudSQL (GCP)
# But the app just sees a Postgres endpoint
}
4. Our Recommendation: "Primary + Failover"
Don't split your app 50/50 across clouds. It's a latency and billing disaster.
Do this instead:
- Pick a Primary: Go all-in on AWS (for example). Use Spot instances, RIs, and deep optimization.
- Architect for Portability: Use Containers, Postgres, and Terraform. Avoid proprietary triggers (like Lambda triggered by Dynamo Streams).
- Keep a "Pilot Light" on Secondary: Have a minimal K8s cluster on GCP with data replication enabled.
- Test the Failover: Once a quarter, try to spin up the full stack on GCP.
Strategy first. Cloud second. Lock-in is a business risk calculation, not just a technology choice. Sometimes, being locked into AWS is worth the 30% velocity gain. Just make that choice consciously.
Tagged with
Need help with your infrastructure?
Book a free architecture review and get expert recommendations.
Book Architecture ReviewCloud Infrastructure & DevOps
Read Next

Stop clicking in the console. Learn the 5 non-negotiable best practices for scaling your Infrastructure as Code using Terraform.

Why committing .tfstate to Git is a security disaster. A guide to setting up robust S3+DynamoDB remote backends with encryption and locking.
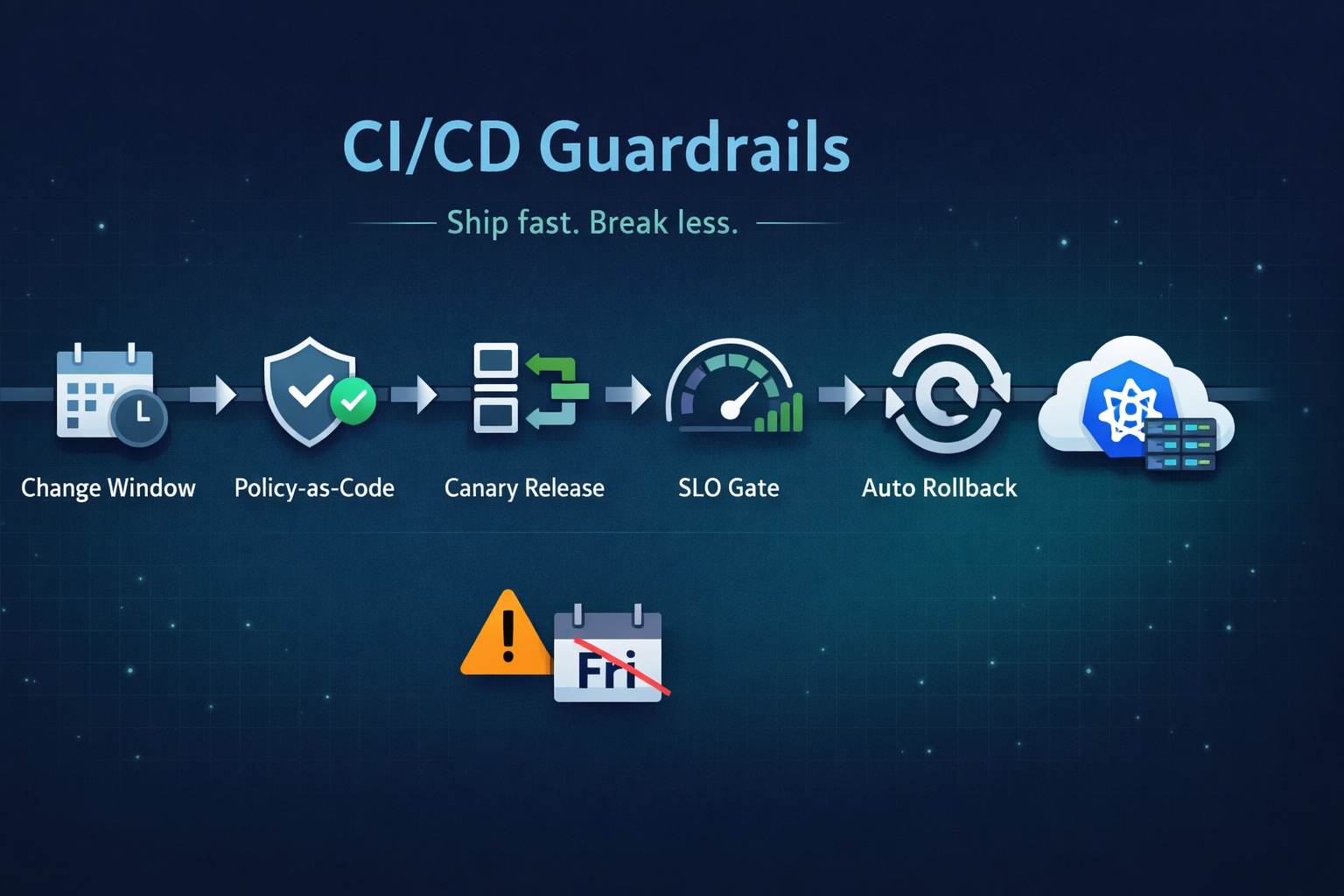
Ship fast without breaking prod. Our 5 guardrails: change windows, policy-as-code, canary releases, SLO-based gating, and automated rollback.